For a Money Laundering Reporting Officer (MLRO), the greatest threat to a compliance program is not a lack of data—it is an overwhelming abundance of statistical noise. In 2026, standard legacy screening pipelines operate at a catastrophic 90% to 95% false-positive rate.
When your team is forced to manually review thousands of name collisions against OFAC or global PEP lists, you trigger a brutal internal conflict. Your analysts suffer from severe Alert Fatigue, increasing the risk of a catastrophic False Negative (approving a real sanctioned entity). Meanwhile, your Chief Marketing Officer (CMO) is furious because legitimate users are stuck in a 24-hour manual review queue, destroying your Customer Acquisition Cost (CAC) and onboarding conversion.
To protect both your regulatory license and your platform's growth, compliance officers must transition from brute-force manual reviews to strategic, automated triage. Here are three critical strategies to handle AML false positives at the infrastructure level.
Strategy 1: Automated Triage via Secondary Identifiers
The foundational error of legacy screening is relying on isolated string matching (e.g., flagging any user named "Mohammed Ali" or "John Smith"). Human names are not unique identifiers.
Following the FATF’s Risk-Based Approach (RBA), your compliance architecture must automatically cross-reference Secondary Identifiers before an alert ever reaches a human dashboard.
If a user triggers a name collision against a sanctions list, your API should immediately query the user's validated KYC profile for secondary metadata:
- 🔹 Date of Birth (DOB)
- 🔹 Nationality and Geolocation
- 🔹 National ID or Passport Number
If the sanctioned entity was born in 1965, and your newly registered user was born in 1998, the system should execute an automated, auditable dismissal. Analysts should only be notified when multiple secondary identifiers align with the watchlist profile.
Strategy 2: Intelligent Suppression in Perpetual KYC (pKYC)
The shift toward Perpetual KYC (pKYC) and continuous monitoring means your user base is screened daily against updated watchlists. Without intelligent suppression, a user who triggers a false positive today will trigger the exact same false positive tomorrow.
If an analyst spends 15 minutes investigating a flagged user, verifies their identity, and clears them, that decision must be permanently mapped to that user’s data signature.
Implementing Intelligent Suppression Memory (dynamic whitelisting) ensures that when this cleared user initiates a new transaction or gets scanned during continuous monitoring, the system remembers the previous clearance.
Legacy Manual Review vs. Strategic Automated Triage
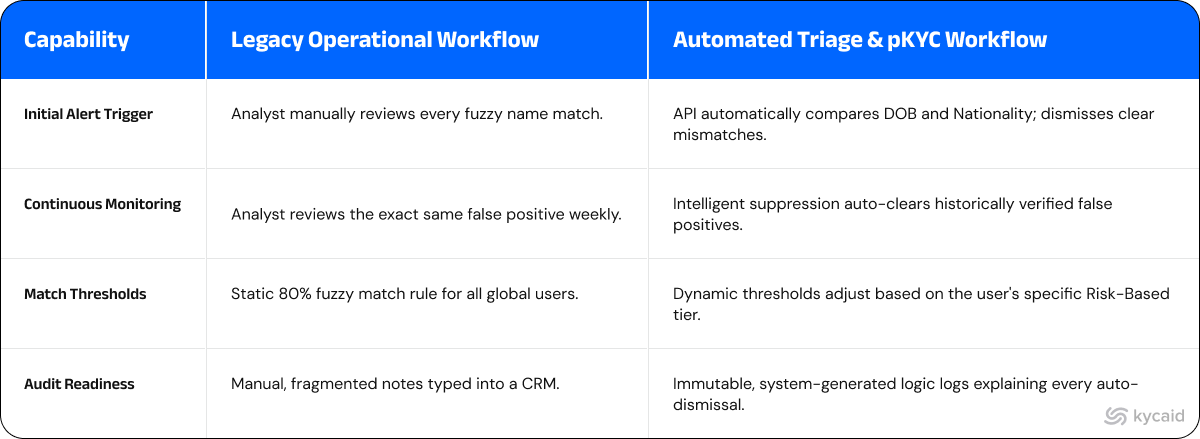
Strategy 3: Dynamic Risk Escalation
Applying a rigid, static match threshold to your entire global user base guarantees an unmanageable queue. Your screening thresholds must reflect the actual risk of the transaction.
Compliance officers must implement Dynamic Risk Escalation. If a retail user is registering from a low-risk jurisdiction and passing iBeta L2 biometric liveness, the fuzzy-matching threshold for their name should be extremely tight (e.g., requiring a 95% exact match to trigger an alert).
Conversely, if a corporate entity (KYB) is executing a $50,000 cross-border wire transfer, the system should dynamically widen the net, escalating even partial semantic matches for immediate manual review in your case management system.
The KYCAID Solution: Infrastructure-Level Alert Resolution
Implementing these FATF-aligned strategies manually requires massive engineering resources. KYCAID is built to execute this operational playbook out-of-the-box. We do not just pass raw alerts to your MLRO; we resolve the noise programmatically.
Our screening engine runs multi-field matching across first name, last name, middle name, and date of birth simultaneously, rather than relying on a single name string. This alone eliminates the bulk of false positives that plague systems built on isolated name matching.
Once a person or document has been matched and reviewed, KYCAID automatically excludes them from future monitoring cycles. Your analyst clears the case once — the system remembers it permanently. No duplicate alerts. No wasted review hours. This is intelligent suppression built into the core workflow, not bolted on as an afterthought.
Every client operates with their own screening configuration — matching thresholds, list selection, and risk parameters are tailored to your specific compliance requirements and jurisdiction. There are no one-size-fits-all ruleset forced onto your pipeline.
The result: your MLRO receives only actionable alerts. Your onboarding stays fast. And your FinOps team stops paying analysts to clear the same false positive twice.
Stop burning your FinOps budget on irrelevant alerts.
FAQ
How do secondary identifiers reduce AML false positives?
Secondary identifiers (like Date of Birth and Nationality) provide essential context. By automatically comparing these data points against the metadata of the sanctioned entity, a compliance system can programmatically dismiss alerts where the names match but the underlying identities clearly do not.
What is Intelligent Suppression in pKYC?
Intelligent suppression (or dynamic whitelisting) is a feature vital for Perpetual KYC (continuous monitoring). It remembers when an analyst manually clears a false positive. If that same legitimate user triggers a scan during future updates, the system automatically suppresses the alert, preventing duplicate manual reviews.
Why is Alert Fatigue dangerous for compliance teams?
Alert fatigue occurs when analysts are overwhelmed by a massive volume of false positives. This cognitive overload leads to complacency, significantly increasing the risk of a "False Negative"—where an analyst accidentally approves a real criminal or sanctioned entity, leading to severe regulatory penalties.